Say no to zero-day attacks
Your home computer is vulnerable to zero-day attacks. This is because the programs you use so often have vulnerabilities that cybercriminals can then then quickly exploit to compromise your computer system. Patches are available to fix vulnerabilities, but often not fast enough to stop attacks. Sophos Home, however, is uniquely ready to stop zero-hour attacks.
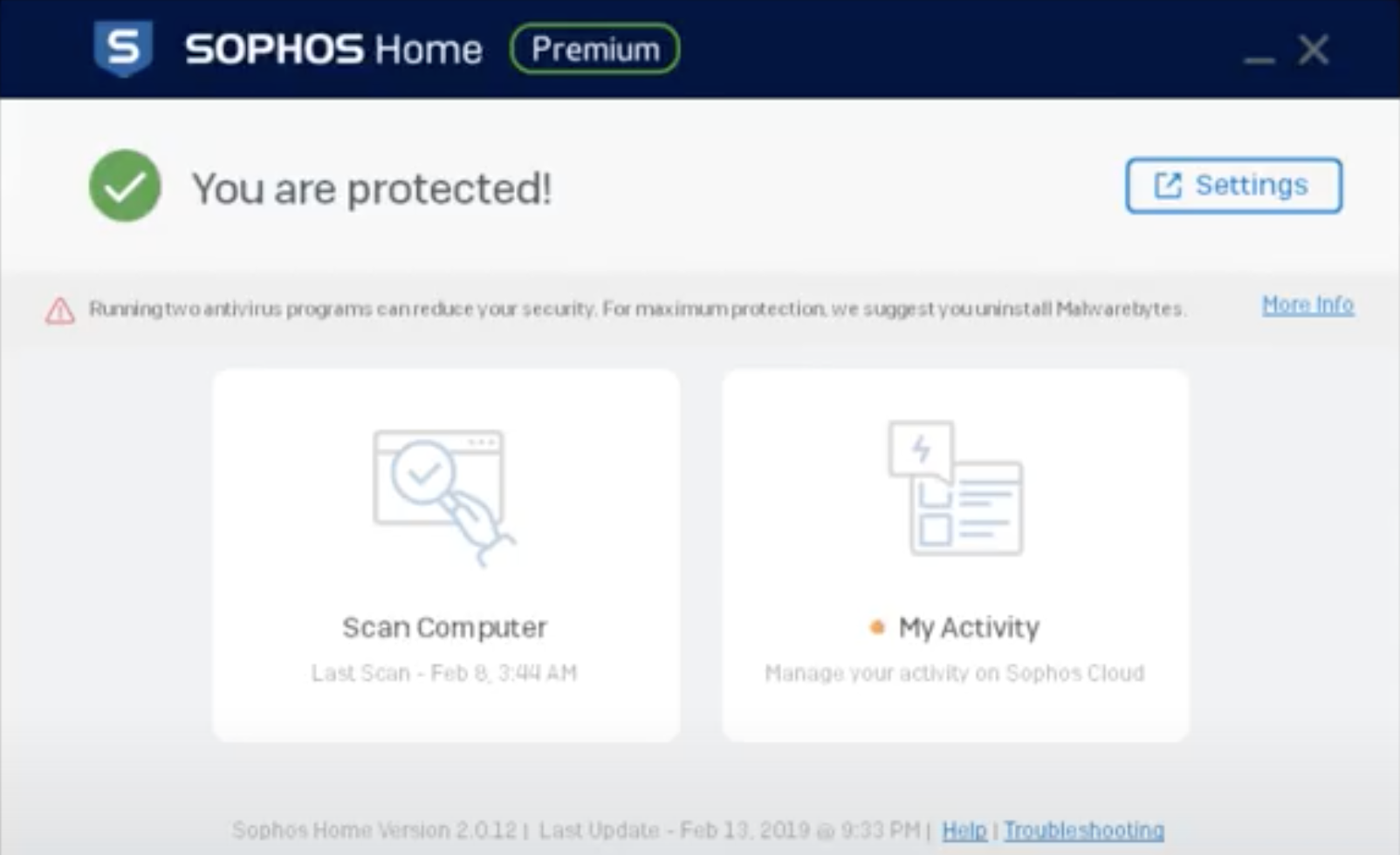
Sophos Home protects home computers from zero-day attacks by leveraging AI with deep learning to evaluate files before they run. It then blocks and removes files that are suspicious. The intuitive capabilities of Sophos Home helps identify brand new, never-before seen threats like a zero-day attacks.
With features like real-threat prevention, process privilege escalation, APC protection, credential theft protection, and more, Sophos Home ensures your home computers are safe from advanced malware and hacking attacks. You can use your PCs and Macs in peace, knowing your home computer is protected by business-grade cybersecurity.